Decrypted: How bad was the US Capitol breach for cybersecurity?
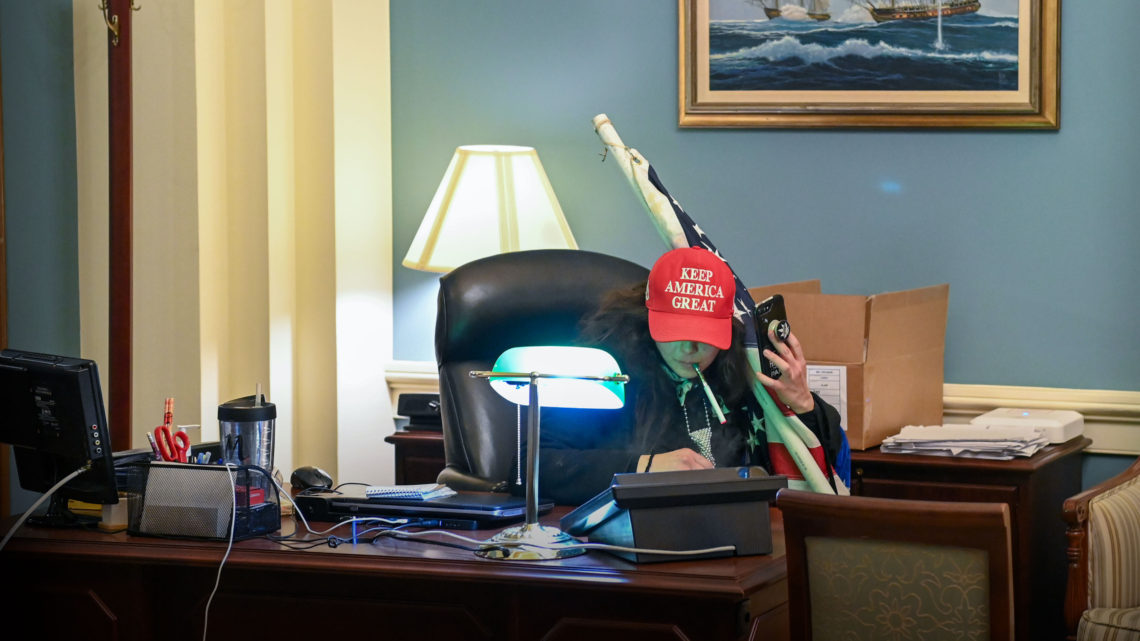
January 11, 2021It’s the image that’s been seen around the world. One of hundreds of pro-Trump supporters in the private office of House Speaker Nancy Pelosi after storming the Capitol and breaching security in protest of the certification of the election results for President-elect Joe Biden. Police were overrun (when they weren’t posing for selfies) and some lawmakers’ offices were trashed and looted.
As politicians and their staffs were told to evacuate or shelter in place, one photo of a congressional computer left unlocked still with an evacuation notice on the screen spread quickly around the internet. At least one computer was stolen from Sen. Jeff Merkley’s office, reports say.
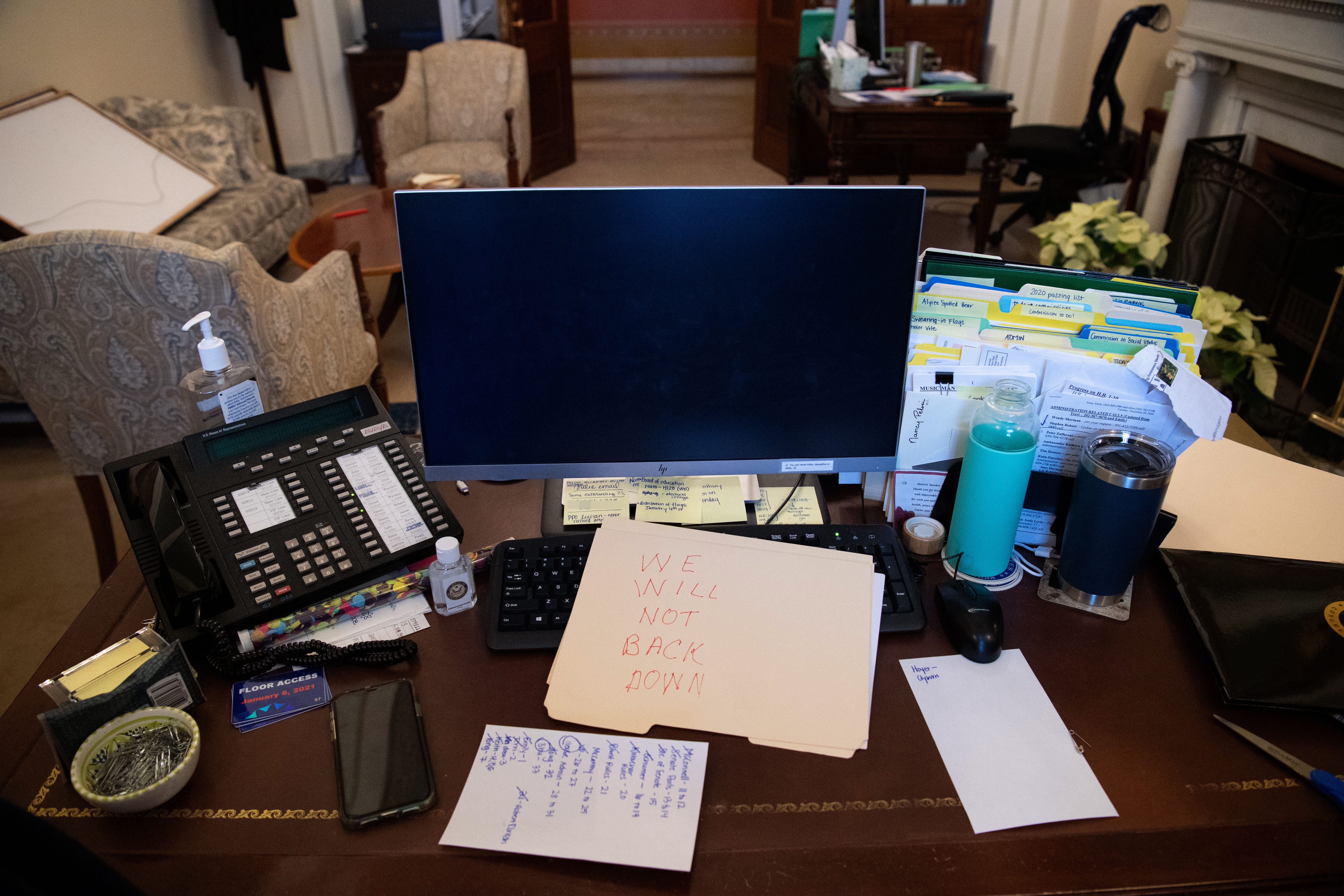
A supporter of U.S. President Donald Trump leaves a note in the office of U.S. Speaker of the House Nancy Pelosi as the protest inside the U.S. Capitol in Washington, D.C, January 6, 2021. Demonstrators breached security and entered the Capitol as Congress debated the 2020 presidential election Electoral Vote Certification. Image Credits: SAUL LOEB/AFP via Getty Images
Most lawmakers don’t have ready access to classified materials, unless it’s for their work sitting on sensitive committees, such as Judiciary or Intelligence. The classified computers are separate from the rest of the unclassified congressional network and in a designated sensitive compartmented information facility, or SCIFs, in locked-down areas of the Capitol building.
“No indication those [classified systems] were breached,” tweeted Mieke Eoyang, a former House Intelligence Committee staffer.
Hi, former HPSCI staffer here.
Congressional offices deal in unclassified information. Most of the things they deal with are open source.
Classified information dealt with in designated Congressional SCIFs. No indication those were breached. https://t.co/Ciel6BW3oU
— Mieke "18 USC 2383" Eoyang (@MiekeEoyang) January 7, 2021
But the breach will likely present a major task for Congress’ IT departments, which will have to figure out what’s been stolen and what security risks could still pose a threat to the Capitol’s network. Kimber Dowsett, a former government security architect, said there was no plan in place to respond to a storming of the building.
My heart goes out to the unsung IT heroes at the Capitol tonight. My guess is they’ve never had to run asset inventory IR before – a daunting, stressful task in a tabletop exercise – and they’re running one (prob w/o a playbook) following a full on assault of the Capitol.
— socially distant, mask wearing bat (@mzbat) January 7, 2021
The threat to Congress’ IT network is probably not as significant as the ongoing espionage campaign against U.S. federal networks. But the only saving grace is that so many congressional staffers were working from home during the assault due to the ongoing pandemic, which yesterday reported a daily record of almost 4,000 people dead from COVID-19 in one day.
THE BIG PICTURE U.S. blames “ongoing” federal agency breaches on RussiaRead more: feedproxy.google.com
A quick note about the reviews I do on this site. The product vendors may give me access to their products for free in order for me to do my review, alternatively, I may have bought the product myself. However I make no promises to vendors regarding what I write in my review. Should you click a link that takes you to a sales page for a paid product for sale this link will be an affiliate link and I will be paid a percentage of the sales price should you decide to invest in it.